The ransomware attack on the nation’s biggest fuel pipeline is pressuring officials to address how to stop debilitating hacks.
The Colonial Pipeline Co. Pelham junction and tank farm in Pelham, Alabama.
(Bloomberg) — The ransomware attack that shut down the nation’s biggest fuel pipeline prompted an all-too-familiar question in the corridors of power in Washington and boardrooms across the country: Can anyone stop debilitating hacks?
The recent assault on Colonial Pipeline Co. was a particular affront. Not only did it disrupt fuel distribution on the East Coast, but it also followed an effort by the Biden administration to act against cybercrime — especially ransomware, where criminals remotely disable a computer system and demand payment. Colonial was hit on day 37 of a 60-day push by the Department of Homeland Security to confront such attacks.
The administration’s campaign is the latest in a long series of cyber strategies offered by presidents and lawmakers from both parties to curb hackers. For years, security experts have offered concrete recommendations for governments, companies and other organizations to follow to ward off cyberattacks, but they’re often ignored or punted in favor of more pressing concerns.
“There has to be a different way of approaching this if we are going to stop this plague,” said Philip Reiner, chief executive officer of the Institute for Security and Technology. Reiner’s group recently offered 48 actions the Biden administration and the private sector could pursue against ransomware.
The Colonial Pipeline was idled for the third consecutive day on Monday, May 10, as fuel suppliers increasingly worry about the possibility of gasoline and diesel shortages along the U.S. East Coast. The company said Monday it expects the pipeline to be “substantially” back in operations by the end of the week.
While President Joe Biden recently imposed sanctions on Russia over the hack of SolarWinds Corp., the threat of retaliation or prosecution from the U.S. holds little deterrence — at least so far. Many criminal hackers reside in countries that ignore them or tacitly approve of their behavior. Actions to punish state-sponsored hacking groups, including sanctions and indictments, have previously done little to counter the assaults.
The list of recent cyberattack targets reflects both the sophistication and brazenness of the hackers. In government, the victims include the Department of Homeland Security, the Illinois Attorney General’s Office, even the Washington, D.C., police department. In the private sector, hackers infiltrated big tech companies like Microsoft Corp., the cybersecurity firm FireEye Inc., San Diego-based Scripps Health and even the Houston Rockets of the National Basketball Association.
While Homeland Security advises critical infrastructure operators on risk management, private industry is still responsible for securing its own networks. The result is uneven protection: Some companies, including major banks, have invested heavily in cybersecurity. But many others have followed a pattern of ignoring or minimizing the need for safeguards, which can be costly and easy to defer.
Recent cyberattacks against Twitter and SolarWinds occurred after security employees warned about weaknesses in the companies’ defenses.
Preventing a ‘cyber 9/11′
The problem is particularly troubling for companies that operate critical infrastructure. Initiatives to enhance the security of the operational controls used to run the U.S. electrical grid and other energy infrastructure are years behind better-known efforts to shield data centers and corporate systems, experts say.
In the federal government, the non-partisan Government Accountability Office alone has issued some 3,300 recommendations since 2010 for agencies to address vulnerabilities, yet at least 750 had not been implemented by the end of last year.
“Although the federal government has made selected improvements, it needs to move with a greater sense of urgency commensurate with the rapidly evolving and grave threats to the country,” the GAO warned in March.
In 2019, Congress created a special group called the Cyberspace Solarium Commission specifically to come up with a better, more comprehensive plan to fight back against major hacks. The commission made 52 legislative recommendations in a report last March; Congress has enacted 25 of them so far; roughly 10 of 30 non-legislative recommendations have been implemented.
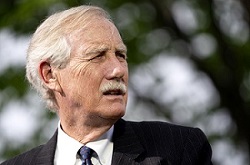
“The Cyberspace Solarium Commission was envisioned to be ‘the 9/11 commission that averts a cyber 9/11,’” the commission’s co-chairs, Senator Angus King, Independent of Maine, and Representative Mike Gallagher, a Wisconsin Republican, said in a statement after the Colonial breach.
“One of the gravest lessons from the terrorist attack 20 years ago was that it was a failure of imagination,” they said. “America can and must be better — we must be imaginative and proactive in navigating the threats of the age of cyber aggression.”
A divided Congress
In the aftermath of the Colonial Pipeline attack, Biden and a bitterly divided Congress will be under pressure to mandate greater disclosure of breaches and costly network protections that have been thwarted in the past.
“My administration takes this very seriously,” Biden said Monday (May 10), as he committed to “a global effort” to combat ransomware attacks, including criminal prosecutions and efforts to disrupt money-laundering operations associated with the hackers.
The White House had already moved to strengthen collaboration between U.S. national security agencies and power utilities, with a plan for rolling out better technology to detect hacks of industrial control systems that run the nation’s power systems.
The administration is also finalizing an executive order that would set basic cybersecurity standards for the federal government, including multifactor authentication of users.
There’s widespread consensus that better coordination between the government and private industry is needed to bolster the nation’s cyber defenses. But it isn’t as easy as it seems.
A major challenge is simply sharing information. The federal government itself is limited in how much it can tell companies about potential threats, and industry leaders have complained they are too often left in the dark.
Despite years of hand wringing about the need for government and companies to collaborate better, “it has yet to really occur,” said Mike McKenna, a former senior White House official with energy and cybersecurity clients.
Coordination deficit
“The industry tends to be impaired because it does not have real-time access to what the government knows, and government tends to be impaired because, with a very few exceptions, they don’t actually have cybersecurity capabilities,” McKenna said.
Companies face numerous obstacles to revealing their own breaches, including fears that they will be slapped with shareholder lawsuits if they disclose an attack too soon. But rapidly informing regulators about possible breaches and the digital fingerprints hackers have left behind can be critical to identifying and preventing other intrusions.
“There are still potential risks that companies take in sharing the information,” said Suzanne Spaulding, a former Homeland Security official who now is a senior adviser at the Center for Strategic and International Studies.
One option for Congress is removing some legal liability, which could encourage companies to disclose cyberattacks swiftly. But if Congress goes too far to shield companies, it could remove pressure for them to harden their defenses, Spaulding said.
“It’s a delicate balance,” Spaulding said. “It’s hard, finding that right formula for maintaining the incentive to do the right thing while figuring out how to incentivize them to share the information.”
James Lewis, senior vice president at the Center for Strategic and International Studies, said people generally don’t take the risk of a cyberattack as incentive enough to take action.
“We’ve been wrestling with this thing for a decade or so now, and the answer is, market forces alone aren’t going to push people to do the right thing,” he said.
“We’ve learned the hard way that there are some basics that make it very hard to get hacked,” Lewis said. “Most people don’t do it.”